Google Cloud Identity
Testiny can be configured to use Google Cloud Identity as your identity provider for single sign-on (SSO). Testiny supports configuring both SSO and email login, or restricting logins by requiring SSO logins. This guide explains how to configure the Google Cloud Identity integration using the OpenID Connect protocol.
Configuring SSO
To configure SSO with Google Cloud Identity, you first need to create a web app integration in Google Cloud Identity and then configure Google Cloud Identity as the SSO provider in Testiny.
Configuration in Google Cloud Identity
If you've already created an OAuth client for Testiny in Google Cloud, then you can skip this section and continue configuring SSO in Testiny.
-
Go to the Google Cloud Console:
https://console.cloud.google.com
Then create a new project for the SSO configuration. -
In your new project, open the side menu (1) as shown in the screenshot below and select
APIs & Services (2) > OAuth consent screen (3).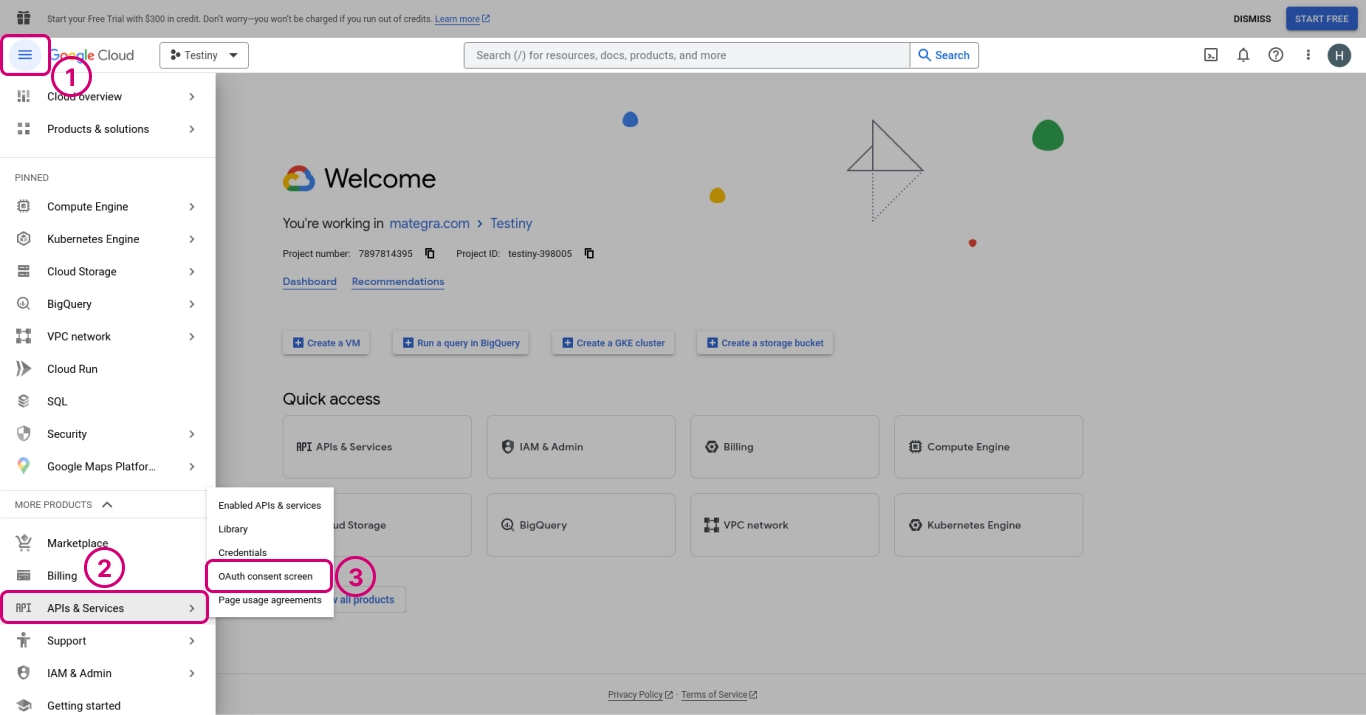
-
Here, select
Internal(1). Then clickCreate(2) to start creating the consent screen.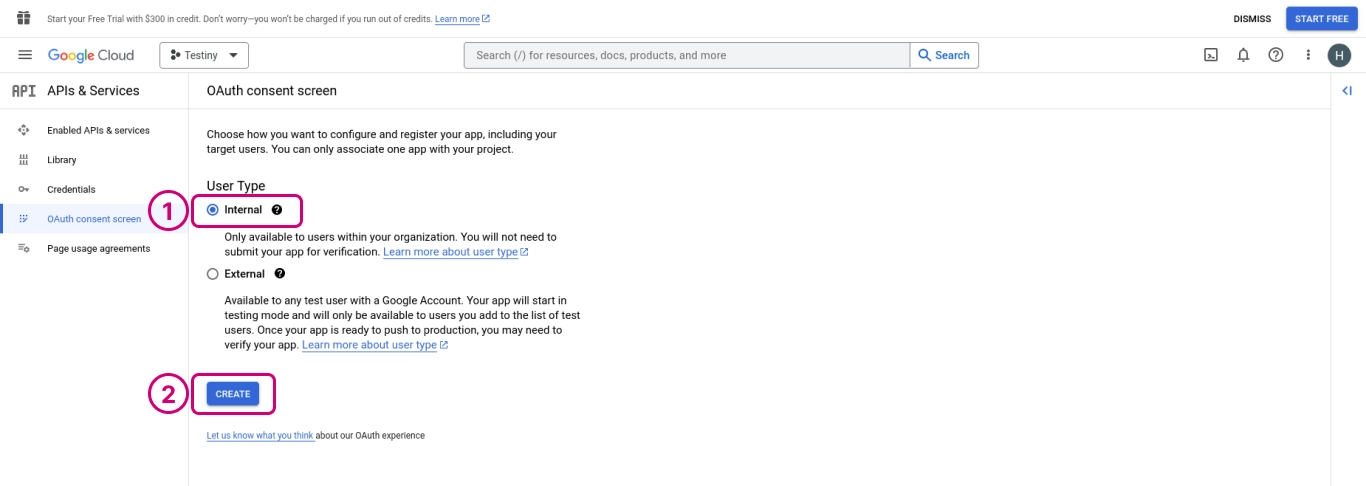
-
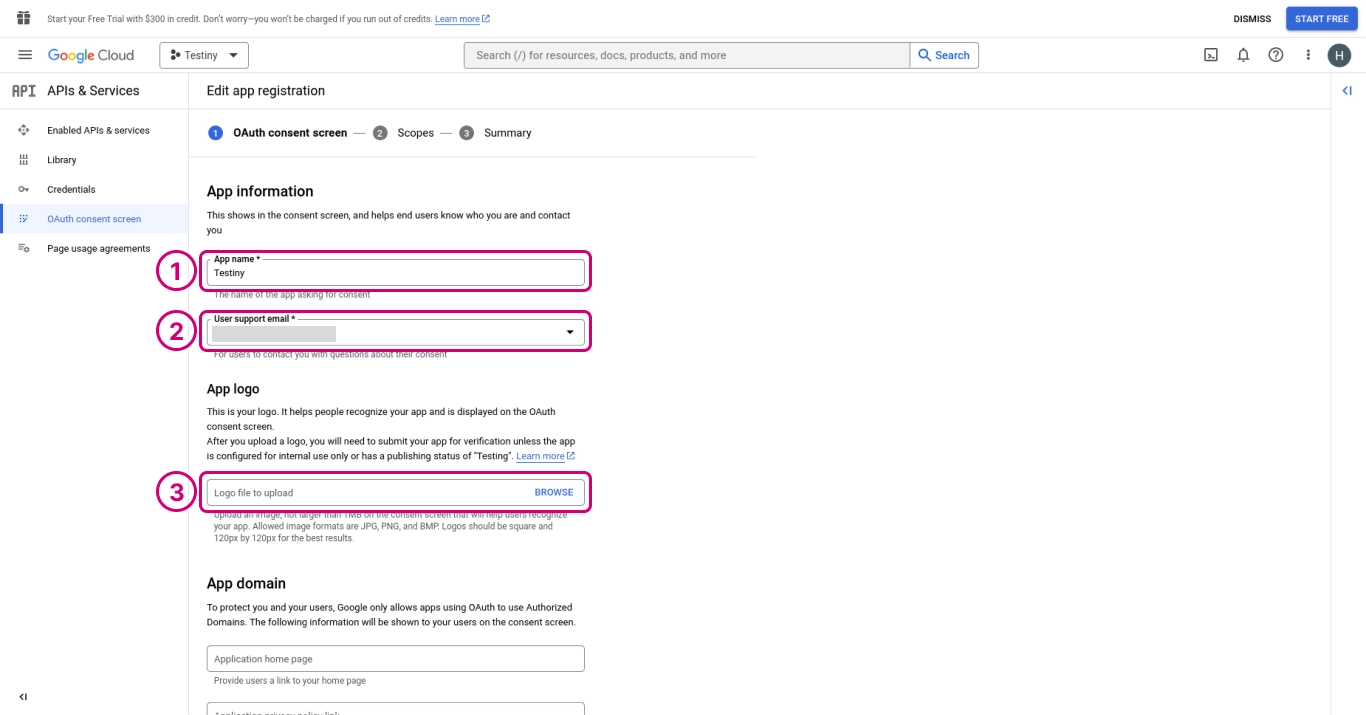
In (1), define the app name, i.e. 'Testiny'.
In (2), choose a user support email.
In (3), you can optionally upload the Testiny logo. You can download the Testiny logo here.
-
Then scroll down and add 'testiny.io' to the authorized domains (1).
In (2), enter an email that will be contacted when there are updates to app integrations.
Then clickSave and continue(3).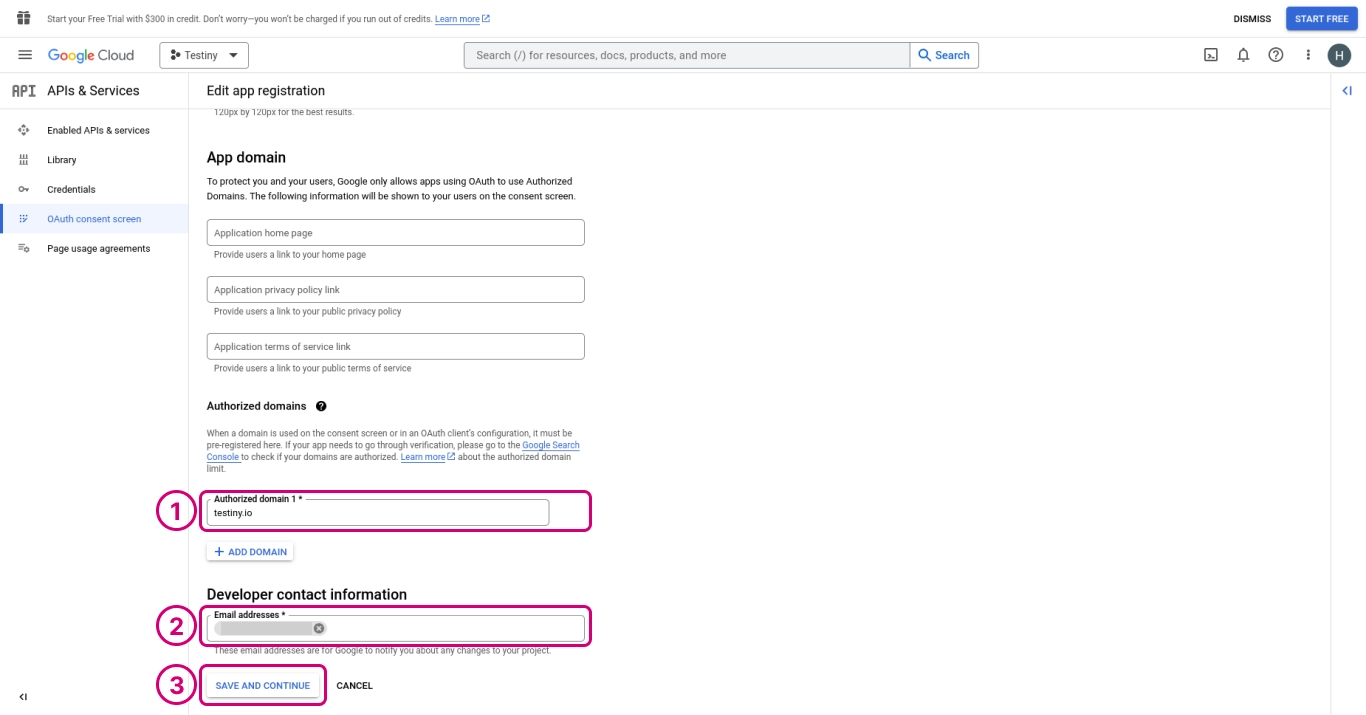
-
Click
Add or remove scopes(1) and in the side panel, check the box foropenid(2).
Then clickUpdate(3) to add the checked values to the allowed scopes.
Then clickSave and continue(4).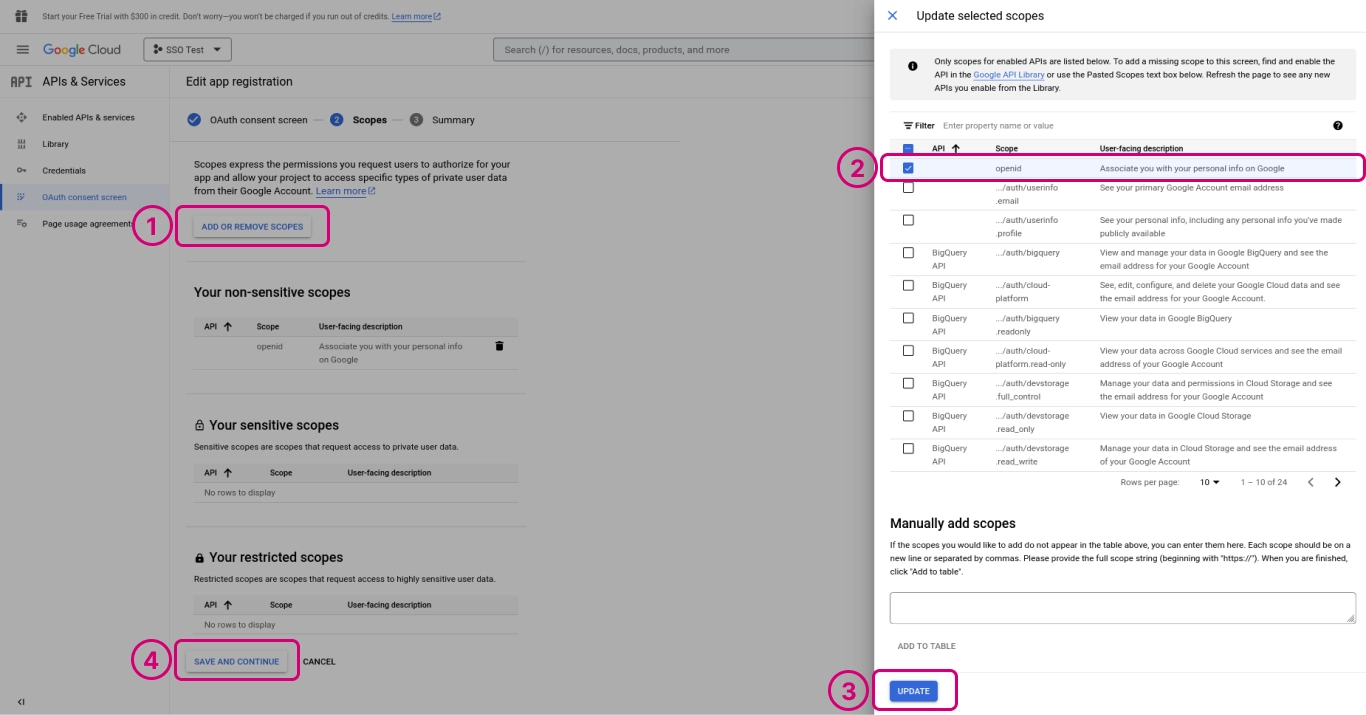
-
Now you're shown a summary of the configuration. Click
Back to dashboard.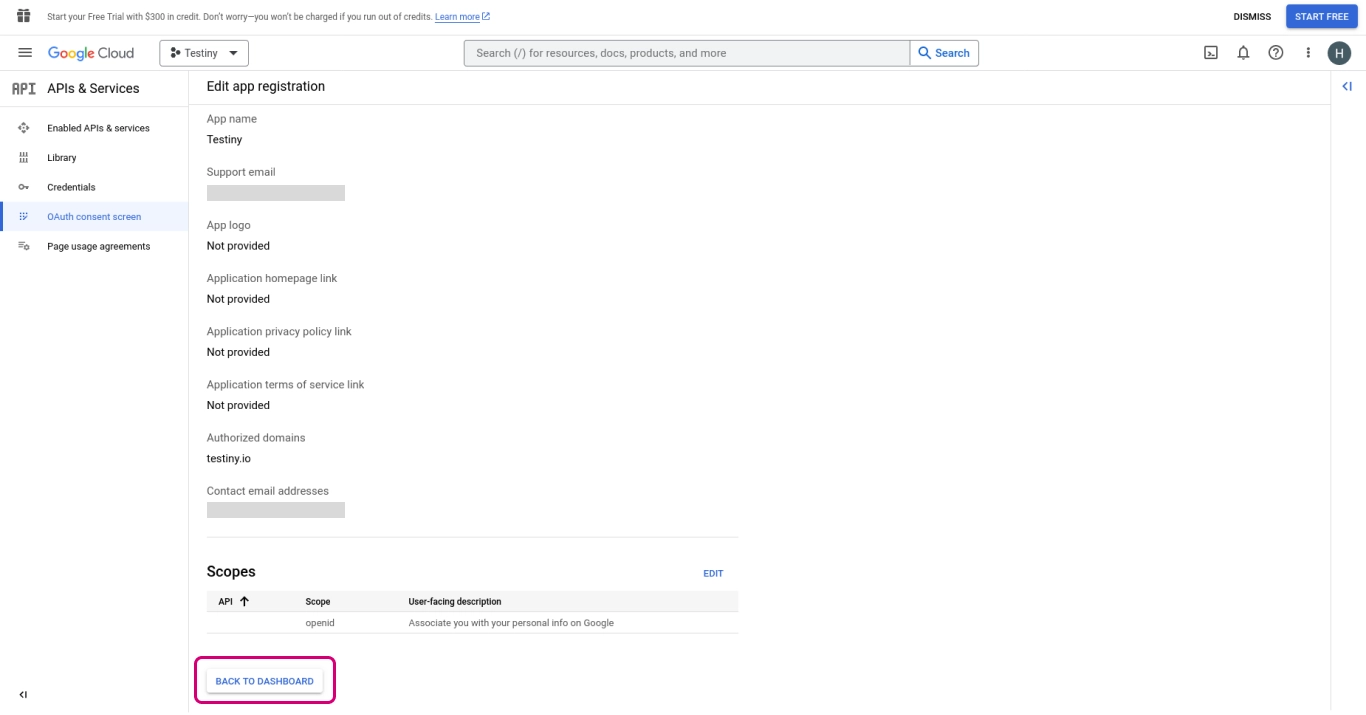
-
Now go to
Credentials(2), click+ Create credentials(2) and chooseOAuth client ID(3).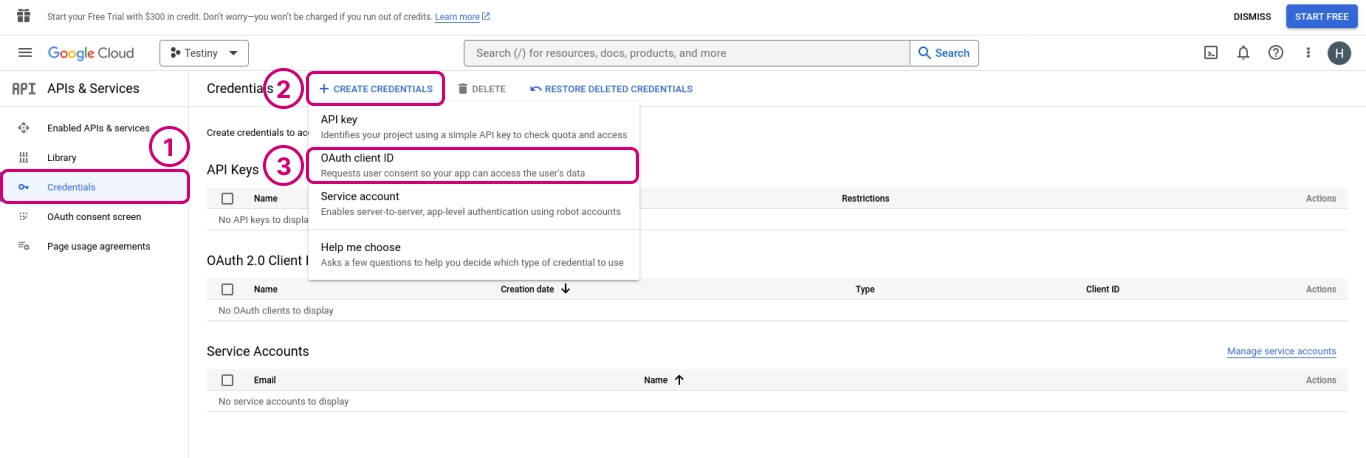
-
In (1), choose
Web applicationas the application type and define a name, e.g. 'Testiny'.
In (2), add the Testiny app URL as an authorized origin:
https://app.testiny.io
In (3), add the following URL as an authorized redirect URL:
https://app.testiny.io/api/v1/oauth/redirect
Then scroll down and clickCreate.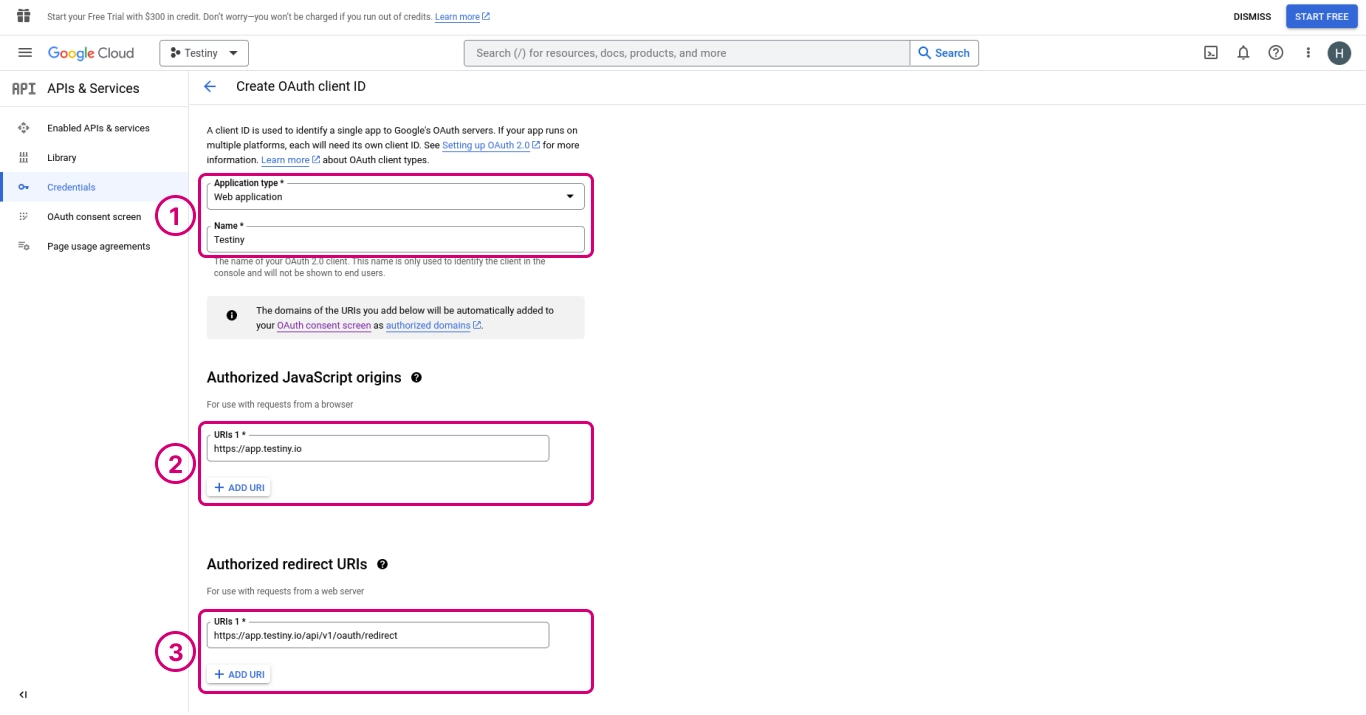
-
Now you've successfully created an OAuth client. In this dialog, please note that you'll need the client ID and client secret in the next step when configuring SSO in Testiny.
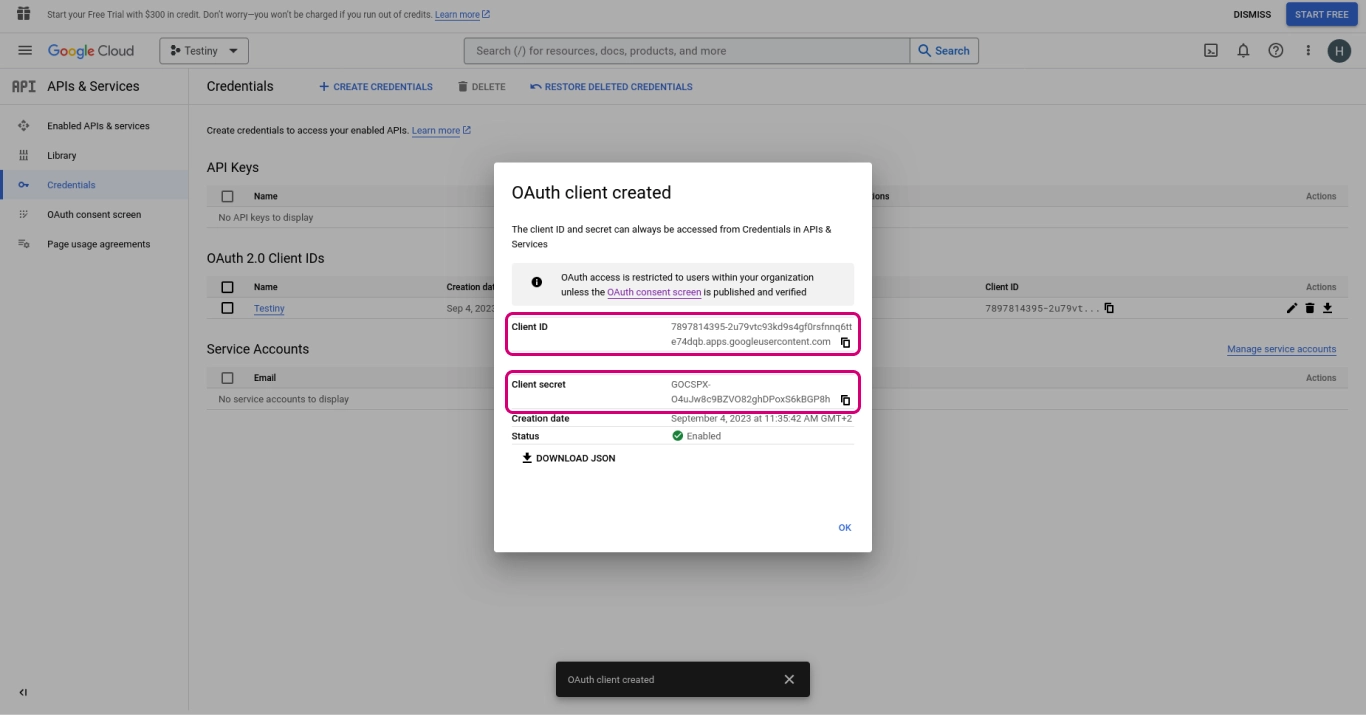
Configuration in Testiny
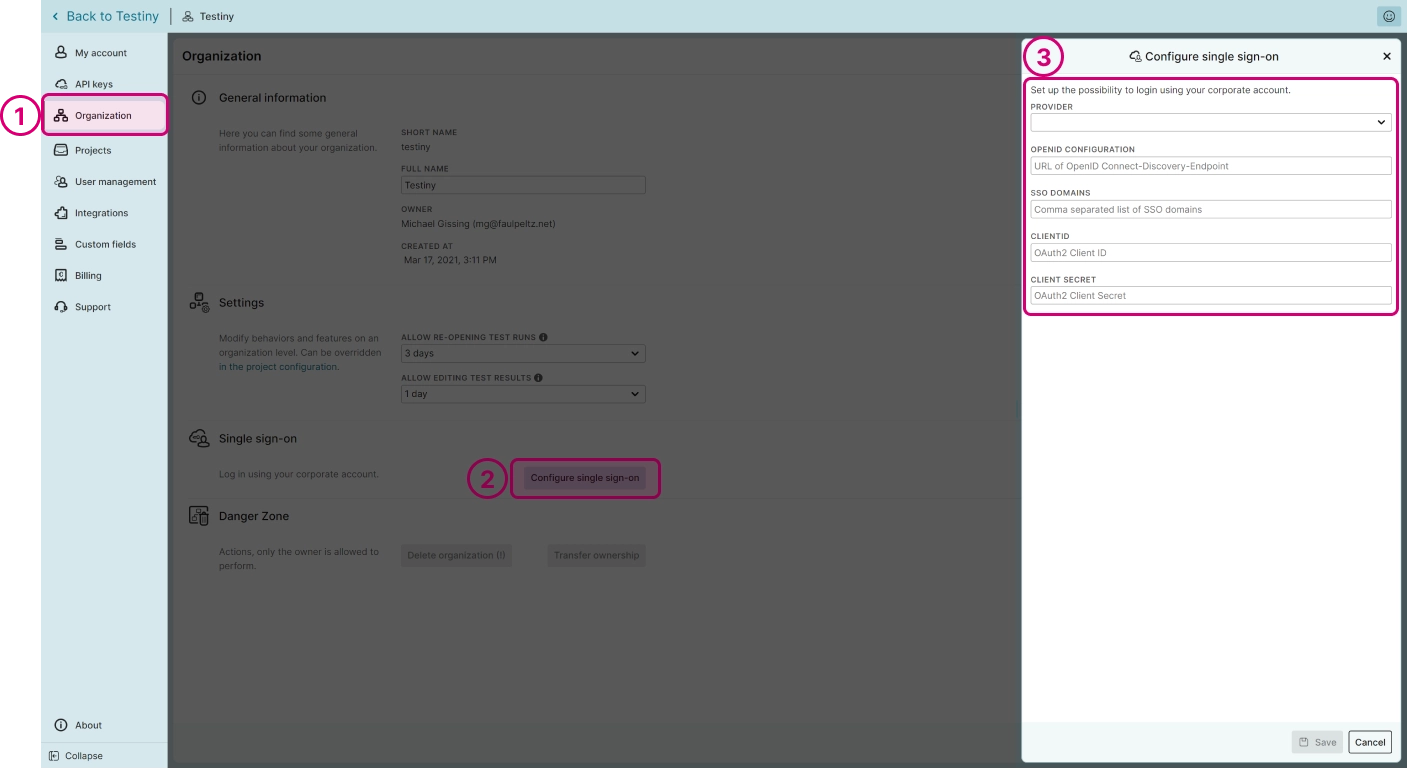
To configure Google Cloud Identity as your SSO provider, you need to have admin rights in Testiny. In Testiny, go to the settings and select Organization (1), as shown in the screenshot below. Click on 'Configure single sign-on' (2). A side panel (3) opens where you need to define the following options:
- Provider — Choose 'Google Cloud Identity' from the list.
- OpenID Configuration — Specify the URL to the OpenID Connect metadata. For Google Cloud Identity, the URL should look like the following example:
https://accounts.google.com/.well-known/openid-configuration. - SSO Domains — Enter the domains that will be able to use single sign-on.
3.1 If you have already invited users from these domains to your Testiny organization, an option will show up to change the login type of these users. By default, the users' login type will be set to "SSO allowed". - Client ID — Enter the client ID of the client created in Google Cloud Identity. You can copy the ID from your app client as described above in the last step in the section on how to configure an app client in Google Cloud.
- Click on "Save". Once SSO is successfull
- Client Secret — Enter the client secret of the client created in Google Cloud Identity. You can copy the secret from your app client as described above in the last step in the section on how to configure an app client in Google Cloud.
- Click on "Save". Once SSO is successfully configured, you can invite SSO users to your organization or update existing users to use SSO login in the user management settings.
To invite users to your organization, navigate to Settings > User management and click the "Invite" button in the top left corner. A side panel will appear, where you can choose whether the SSO login is allowed, required or disabled:
- allowed — the user can log in via SSO, but can also create a password in Testiny and use the email login
- required — the user must log in via SSO
- disabled — the user cannot log in via SSO, only with email login
Then, enter the email address of the user to be added and optionally the first and last name. In the "Role" drop-down, you can adjust the user’s permissions. Learn more about the user management in Testiny.
Logging into Testiny
When SSO is configured in your Testiny organization and the user is invited as an SSO user, they can simply log in to Testiny on the login page. When SSO is required, the user can only log in with SSO. If SSO is allowed but not required, the user might also log in via email and password.
Please note that the owner of the organization in Testiny cannot be restricted to require SSO login so that the owner can always log in with email & password.
Disabling SSO
To disable SSO, go to Settings > Organization and click the next to the configured provider. A dialog will be shown to see which users are affected and cannot log in via SSO anymore. After confirming, SSO is disabled and you continue using email/password login or set up a new SSO provider.
Changing your SSO provider
If you want to modify your SSO configuration or change to another SSO provider, simply click the "Configure single sign-on" button to open the configuration side panel. You can change the SSO provider and set up a new SSO configuration, or add new SSO domains to your current configuration. If you remove an SSO domain, single sign-on may be deactivated for users in this SSO domain.